Security review

GDPR Compliance
As a technology business working with a vast span of industries, we understand the importance of handling data. Our auditing highlights key areas that help you understand your environment and helps define best practices for your business

Valuable Insights
Espok IT Solutions can help identify potential weak points in your Google Workspace security that you may not be aware of and help mitigate these and ensuring that your Google environment is secure.

Prevent Data Leaks
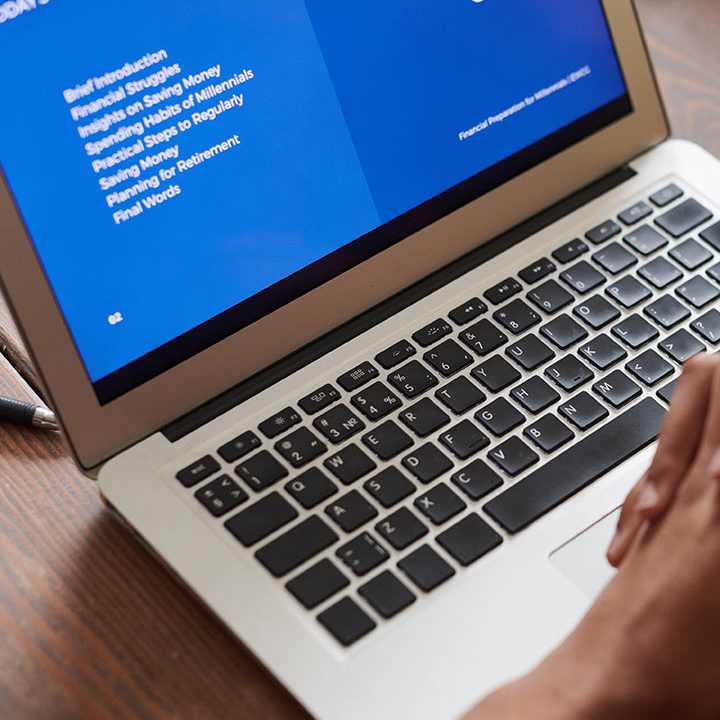
A dongle running Google’s Chrome OS operating system. When placed in the HDMI port of a television or a monitor, this device turns that display into a personal computer or allows it to be used for digital signage.
The Review
These are the main outlines for what we will do for you to help improve your G Suite security.
Consultation
The preliminary audit helps us build a picture of your business to understand the size, technologies used and current operations. This helps us build a road map going forward that fits the needs of the organisation.

Audit
Espok IT Solutions will review your Google Workspace setup. This will always include a review of the users, groups, organisational units, admin roles and domains. However, the security settings audited will be tailored to the organisational needs identified in the consultation.

Review
Once the audit is complete, a report will be sent to you that explains your setup and provides suggestions for improvement.
Action
Espok IT Solutions will now implement the agreed actions to improve the environment. Once all the changes have been applied, we will report back with the benefits and advantages.
After the Review
After we send your report, we will schedule a consultation call with you or your technical team. We will discuss the Google Workspace (formerly G Suite) security issues that may have arisen and we will ask you if you wish to action them yourselves, or if you would prefer for Espok IT to carry them out for you.